Benefits
-
No source code required. Works directly on your firmware
-
Run security checks instantly, as often as you need
-
Detect vulnerabilities early and stay compliant
Built for device developers and security teams
- Embedded developers shipping Linux-based firmware
- Product teams ensuring release readiness
- Security teams triaging CVEs and automating SBOMs
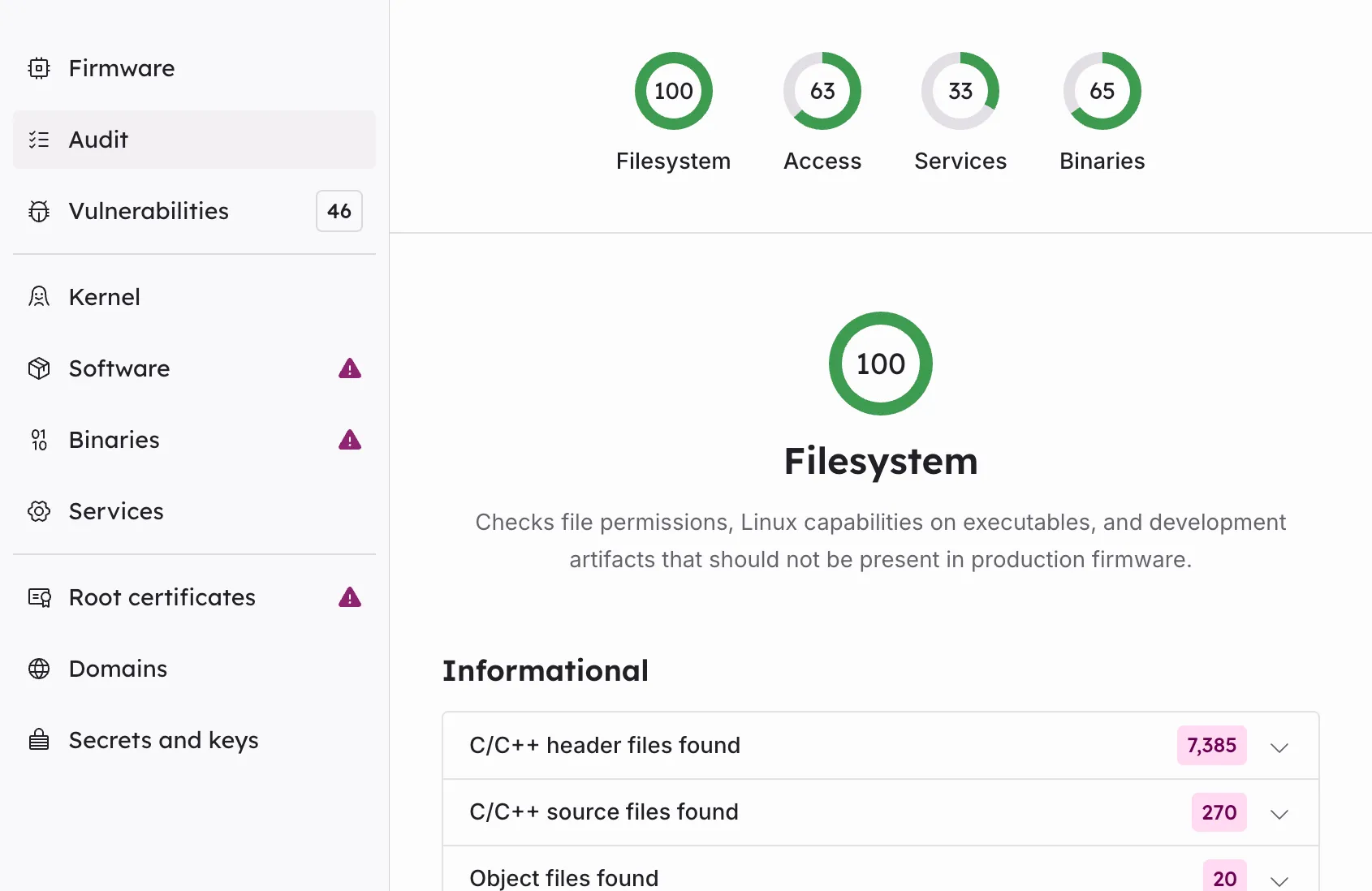
In-Depth Firmware Analysis
- SBOM Generation
- Vulnerability Detection
- Configuration Analysis
-
- TLS Certificate Inspection
- Binary Hardening Analysis
- Kernel Configuration Review
- Remote Endpoint Discovery
- Malware Analysis
Frequently Asked Questions
Here are answers to common questions. If you need more information, please get in touch.
-
What types of firmware images are supported?
Boldwark Firmware X-Ray supports embedded Linux file system archives. We currently support the following container formats:
- Compressed POSIX TAR archives (.tar, .tar.gz, .tar.bz2, .tar.xz)
- ZIP archives (.zip)
More formats can be added as requested.
-
What SBOM components can Firmware X-Ray detect?
Firmware X-Ray identifies a variety of software components, including ELF executables, shared libraries, cryptographic material (such as trusted TLS roots), and critical configurations.
It can also detect and match the following components against vulnerability databases:
- avahi
- bash
- BlueZ
- BusyBox
- bzip2
- curl
- dropbear
- e2fsprogs
- ffmpeg
- glibc
- gnutls
- gpg
- lz4
- systemd
- Weston
We are continually expanding support for more components.
-
Can I integrate Firmware X-Ray with my CI/CD pipeline?
Yes. Firmware X-Ray provides a flexible API for embedding automated firmware analysis directly into your CI/CD workflows. You can trigger scans, retrieve results, and enforce security checks as part of your build or release process so every firmware build is validated before release.
We also provide integrations with select CI/CD platforms, such as GitHub.
-
Does Firmware X-Ray require access to my source code?
No. Firmware X-Ray analyzes compiled firmware images only, not your source code. You gain deep security insights such as vulnerability detection, SBOM generation, and configuration analysis without exposing proprietary code or intellectual property.
-
How can Firmware X-Ray support my regulatory compliance efforts?
Firmware X-Ray supports compliance efforts across a wide range of security and regulatory frameworks, including the Cyber Resilience Act (CRA), NIS2, IEC 62443, and emerging requirements for firmware security and software supply-chain transparency.
It does this by automatically analyzing firmware to:
- identify vulnerabilities
- generate SBOMs
- detect weak configurations
- surface outdated or risky components
- discover hardcoded secrets and other security issues
These insights help you demonstrate security due diligence, validate compliance readiness, and streamline remediation across multiple regulatory obligations.